The most powerful AI-native security tool in the browser
Agents that hunt, detect, and respond. Across every browser you use.

Security at machine speed
Push is AI-native by design. Autonomous agents operationalize robust browser telemetry and real-time control continuously, hunting for new attack techniques, writing detection rules, and deploying blocking scripts across millions of browsers and trillions of events without human intervention.
Our threat research team provides the intelligence that powers the agents. New detections reach customers within minutes of a threat being analyzed.
Attackers are fast. Push is faster.

The modern SecOps stack
Tools focused on the endpoint, network, and inbox are foundational. But attackers opened a new front inside the browser session, a layer those tools weren't built to inspect.
Your CNAPP and ITDR platforms secure your cloud infrastructure and your IdP, but not the browser session. Push secures access to your cloud resources via the browser.
Push Security provides blue teams with net-new visibility of browser-based attacks to complement your existing threat detection & response stack.
EDR doesn’t provide security in the browser layer. Push works alongside your EDR deployment to give you protection at the new layer for attackers.
Proxy based solutions like SSE, SWG, and CASB, see traffic, not what your users see. Push provides in-tab visibility into page structure, scripts, and user interaction.
Hear what people are saying about Push
Today’s security leaders know that defending the browser is key to the future of cyber defense.
Using the Push Platform
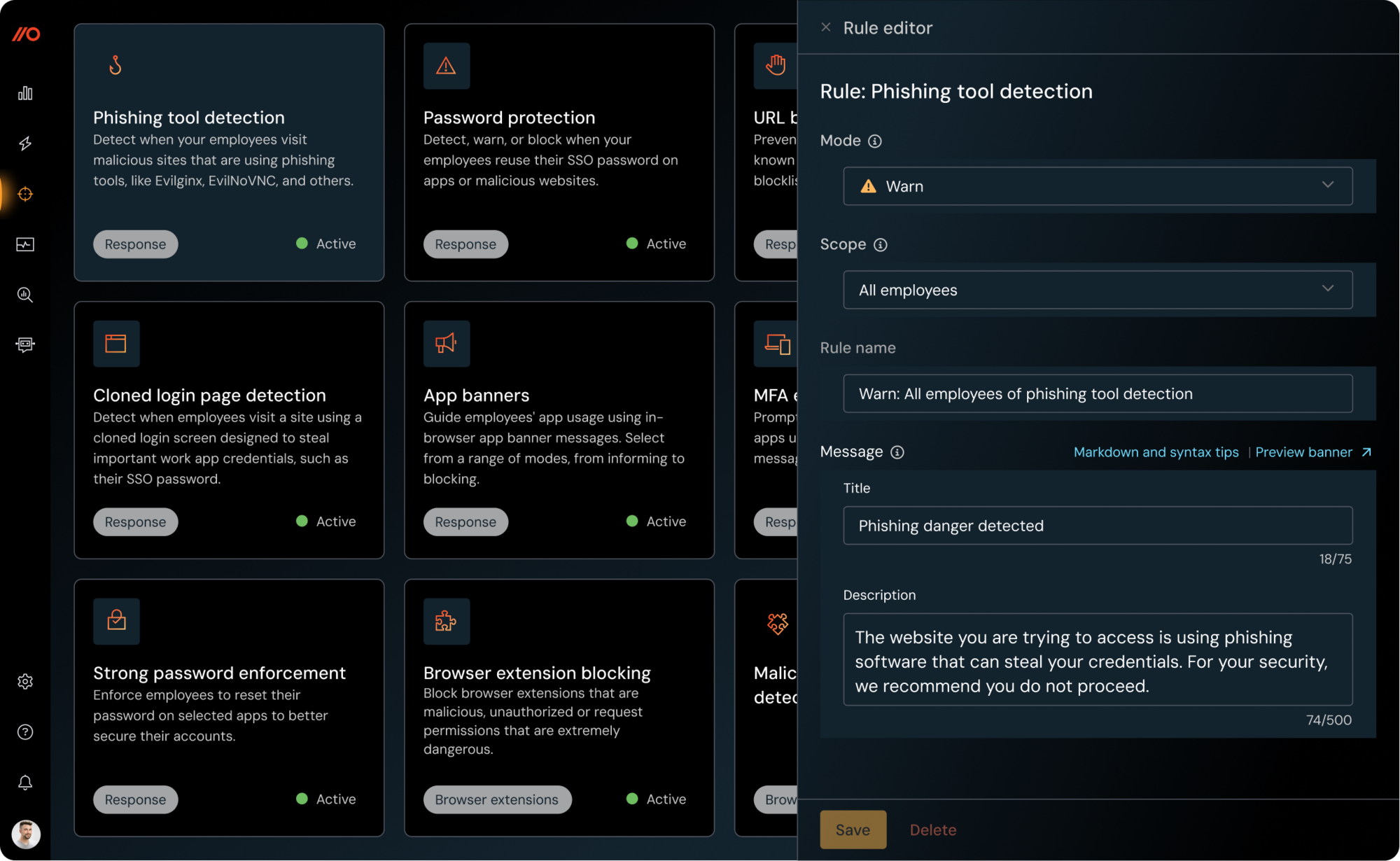
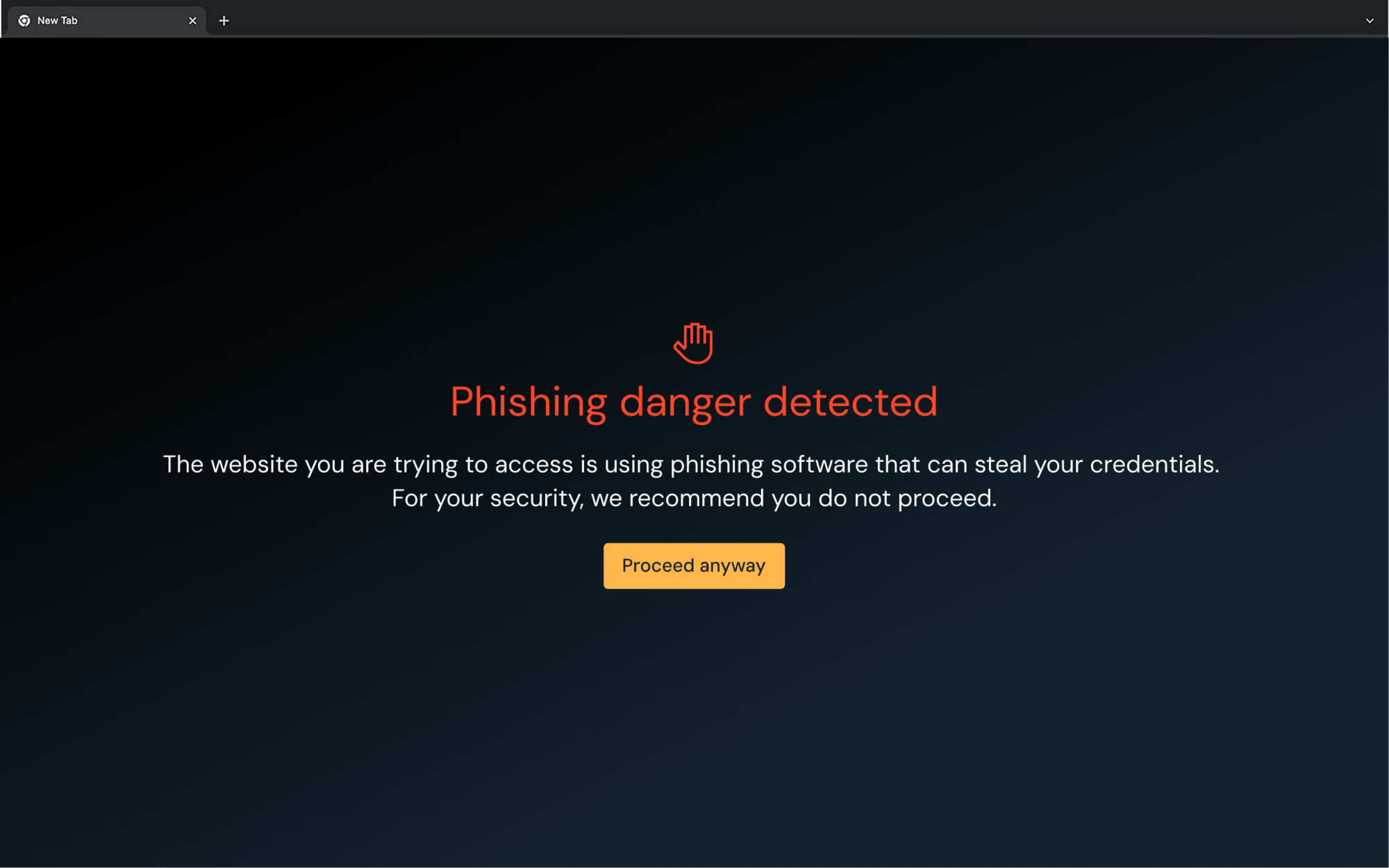
Stop attacks
Secure your organization via the browser.
Detect and block in-browser threats in real time: phishing kits, token theft, and session hijacking. Push inspects page structure, content, and user interaction to spot cloned logins, malicious scripts, and credential misuse as the user sees them.
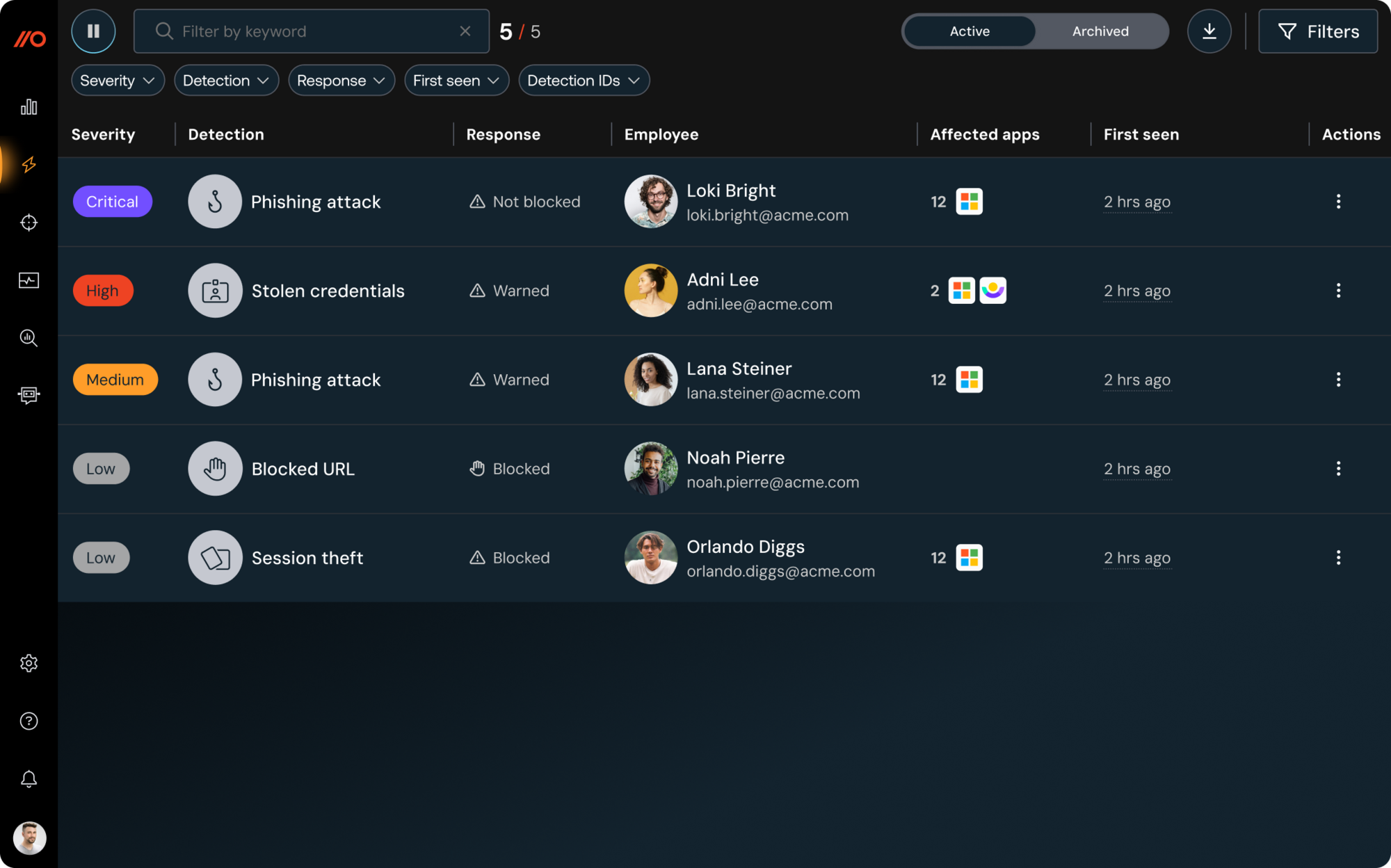
Investigate faster
Detect and respond like never before.
Reconstruct what happened, fast. Push captures page loads, click paths, credential use, and token activity to build user/session timelines, revealing attacker behavior, blast radius, and OAuth exposure.
Protect users
Gaps are everywhere, and attackers are looking for them.
Close common gaps before they're abused. Push flags missing MFA, password reuse, non-SSO logins, shadow apps, and risky extensions, then guides users to remediate or enforces policy in the browser.
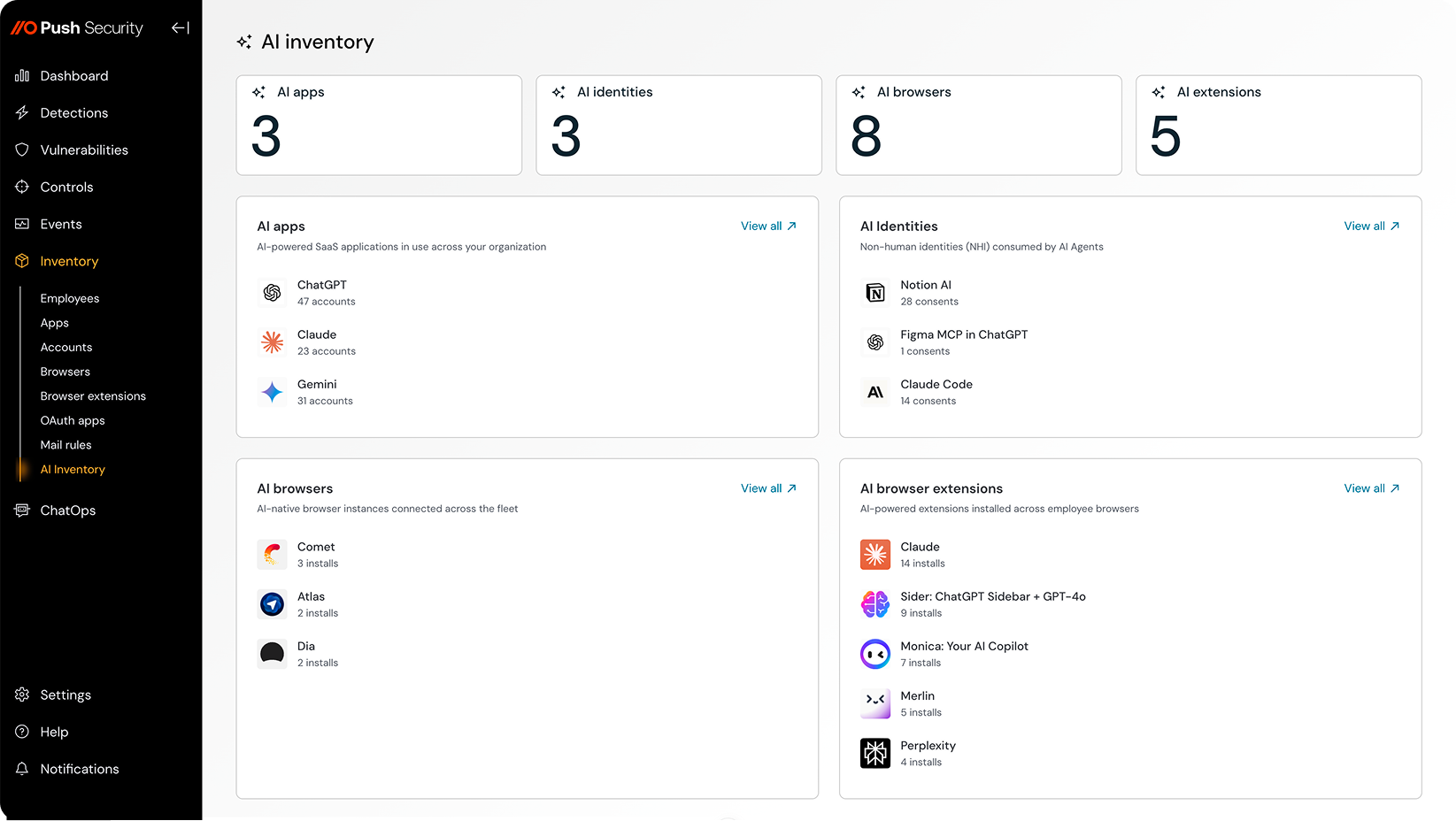
Secure AI use
Your users are already using AI. Now you can see exactly how.
See real user activity inside AI tools: what’s typed, pasted, uploaded, and authorized. From shadow AI apps to agent access and extensions, you get a clear view of where data is going and what’s being exposed, along with controls to act immediately.
One week in and already ahead of attackers
Day Zero
Rapid deployment via MDM, to every browser
Our record: 100k users in 1 hour during normal office hours.

Day One
Instant protection and insights for your users
Stop phishing, session theft, and malware delivery from day 1
Week One
Operationalize with 1st class IdP & SIEM integrations
Harness the power of browser telemetry to fix vulnerabilities and respond to incidents.